 Despite newly revealed cybersecurity flaws in Georgia's statewide touchscreen voting systems; a weeks-long breach by right-wing operatives of the sensitive voting and tabulation software used across the state; and a growing clamor by both the public and state officials for decisive action to try to plug some of these vulnerabilities before next year's Presidential election, all evidence obtained by The BRAD BLOG to date suggests Georgia's Secretary of State has little interest in taking any action at all. At least not before next year's critical contests in the battleground state.
Despite newly revealed cybersecurity flaws in Georgia's statewide touchscreen voting systems; a weeks-long breach by right-wing operatives of the sensitive voting and tabulation software used across the state; and a growing clamor by both the public and state officials for decisive action to try to plug some of these vulnerabilities before next year's Presidential election, all evidence obtained by The BRAD BLOG to date suggests Georgia's Secretary of State has little interest in taking any action at all. At least not before next year's critical contests in the battleground state.
Even if Republican Secretary of State Brad Raffensperger did want to take action, we have learned, he has yet to even begin necessary steps toward state certification of Dominion Voting Systems' newly created software said to remedy some of the recently disclosed cybersecurity flaws. Moreover, well-informed critics argue any software upgrades to the state's touchscreen Ballot Marking Devices (BMDs) would still result in violations of fundamental legal requirements for the state's voting systems.
The path toward nailing down what Raffensperger's office is or isn't doing; what they may or may not do under state law; and what they are or aren't telling the public about all of it has been an odyssey over the past days, amid misleading discussion with a representative of the Secretary's office, contrary information from an official at one of the country's few certified independent voting system test labs, and a curious admission by a representative for Dominion, the state's election system vendor.
The only thing fully clear as of now: Despite calls from cybersecurity and elections experts to mend Georgia's insecure, unverifiable voting systems before next year's Presidential contest, the state insists they will not be upgrading the Dominion voting software until 2025. What has become clearer to us in recent days is that the Secretary of State cannot upgrade the systems legally, at this point, even if he wanted to --- which, evidently, he does not...
The upgrade's downfall
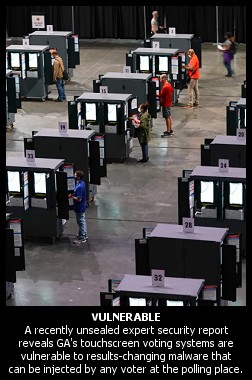 On the heels of last month's long-awaited unsealing of a damning 2021 scientific report by a cybersecurity and voting systems expert informing Raffensperger, the State Election Board, and a federal judge of alarming vulnerabilities in Georgia's statewide voting system, top politicians in the swing-state, both Republican and Democratic, have been calling on the Secretary of State to take swift measures to improve election security.
On the heels of last month's long-awaited unsealing of a damning 2021 scientific report by a cybersecurity and voting systems expert informing Raffensperger, the State Election Board, and a federal judge of alarming vulnerabilities in Georgia's statewide voting system, top politicians in the swing-state, both Republican and Democratic, have been calling on the Secretary of State to take swift measures to improve election security.
As The BRAD BLOG reported exclusively in mid-May, state officials stunned the court at the time when they informed the federal judge overseeing a long-running challenge to the state's touchscreen voting systems that no upgrades to Georgia's more than 70,000 pieces of voting and tabulation equipment would take place until after next year's Presidential election. That, despite both the alarming expert report and a security-imperiling 2021 voting system breach in Georgia's Coffee County.
Top officials from both major parties in the Peach State have been demanding Raffensperger patch the election software --- which the University of Michigan's J. Alex Halderman found in his newly-unsealed report to be rife with vulnerabilities allowing easy insertion of results-changing malware across entire jurisdictions --- with an upgraded version created by Dominion.
But The BRAD BLOG has now confirmed Georgia cannot legally install the new version at this time for multiple reasons. Among them, Raffensperger's office has so far failed to even contract with an approved, independent lab to conduct testing and render a report, mandatory steps toward achieving the state certification required before implementing a new software version.
The upgrade in question, version 5.17 of Dominion's software suite, purportedly addresses some of the security defects Halderman identified in his recently-unsealed 2021 report. The vulnerabilities he documented were confirmed in 2022 by the federal Cybersecurity and Infrastructure Security Agency (CISA), housed at the U.S. Department of Homeland Security.
Upon reviewing the then-sealed Halderman Report last year, CISA found "these vulnerabilities present risks that should be mitigated as soon as possible." The agency issued an alert in June 2022 urging jurisdictions that use Dominion's software --- including the entire state of Georgia --- to upgrade to the newest software, certified to federal standards by the U.S. Election Assistance Commission (EAC) in March of this year.
To legally carry out such an update in Georgia under state law, however, the Secretary of State's office must also undertake state certification for Dominion's 5.17 suite. Georgia mandates voting devices undergo not only federal certification by the EAC, but state certification as well, after state-specific testing conducted by an independent testing agency. To date, the new software has received no such state certification.
The normally technocratic, behind-the-scenes process has outsized implications for the rest of the country due to Georgia's Presidential battleground status. The Peach State will hold its 2024 Presidential primaries in early March.
A central wrench holding up the works: the Secretary of State has not formally designated an independent Georgia Certification Agent, as required when updating software versions. Such agents render reports attesting to a voting system's legal compliance prior to the Secretary's state-level certification.
The Lab Director at the voting system test laboratory Georgia used for certification testing in 2019, Pro V&V, tells us the firm has no contract with Raffensperger's office --- and hasn't even been contacted by them regarding the new software.
On Friday, we asked Secretary of State spokesperson Mike Hassinger for the name of the state's certification agent. His answer? "I have no idea!"
He later emailed to emphasize he would do his "best to find out," claiming that state certification processes "are underway" --- but if so, the evidence for that so far is scant.
Hassinger's boss, Raffensperger, has been taken to task of late in the court of public opinion for refusing to harden the cybersecurity holes found in his $150 million computerized voting equipment purchased just before the 2020 elections. Now, with no independent testing authority at hand to conduct the state-mandated review, Raffensperger's office couldn't update to the latest Dominion software even if he wanted to ... unless, for instance, as one source speculates, the office cobbles together a legally dubious internal review, renders a report to itself, and then certifies. That, however, would be akin to grading one's own schoolwork.
In the meantime, Jack Cobb, the Pro V&V Lab Director, said that, while he hasn't read the state's legal code in about a decade and isn't a lawyer, "I don't think GA Election Code allows an internal review."
'Tough noogies'
Hassinger is the Secretary of State spokesperson known for recently declaring "tough noogies" to Politico as part of an attempted belittling attack on "the PhDs" critiquing Georgia election software. He likened them to far-right "paranoiacs and conspiracists" such as MyPillow CEO and disinformationist Mike Lindell. The office has charged that, like Lindell, the longtime cybersecurity professors are out of touch with the state's supposedly iron-clad physical security measures --- measures the Secretary's office claims will prevent any voting system malfeasance during next year's elections.
The spokesperson emailed us on Monday to say the "state certification agent who conducts certification testing is Pro V&V." But Pro V&V's Cobb maintained that his company has "not been contacted" by the state in regard to the new Dominion software.
Furthermore, Hassinger misleadingly insisted that Pro V&V has "conducted testing for Democracy Suite version 5.17 and provided a copy of that report as part of the Secretary's state certification process, which remains underway."
But Hassinger failed to supply any such report as requested, as we repeatedly made clear that we were inquiring about state certification, a wholly separate process from the EAC's federal testing. The two processes cannot be conflated. Pro V&V did work on federal testing of the new software for EAC certification, but not for the state of Georgia's separate certification process, a distinction Cobb immediately understood.
Make no mistake, we have confirmed through Pro V&V that the Secretary of State did not provide the testing lab with a contract, nor even reach out to them about 5.17, let alone receive a state certification report from the lab. That's according to Cobb himself, who told us: "Pro V&V has not been contacted nor contracted to test 5.17 for the SOS for certification to the GA state requirements."
So, tough noogies, but someone is apparently trying to mislead the public here.
Back to the breach
 To update the election computers in response to J. Alex Halderman's report, the Secretary of State's office has no Dominion option besides 5.17 if it wants to continue using unverifiable BMDs for the 2024 election. Yet, without a positive report from a Georgia certification agent, the office has no viable way to state-certify Dominion's latest iteration.
To update the election computers in response to J. Alex Halderman's report, the Secretary of State's office has no Dominion option besides 5.17 if it wants to continue using unverifiable BMDs for the 2024 election. Yet, without a positive report from a Georgia certification agent, the office has no viable way to state-certify Dominion's latest iteration.
That means ignoring Halderman's report --- as well as the high-profile Georgia politicians recently citing its revelations --- and simply sticking with the present iteration, version 5.5-A, for next year's elections. 5.5-A is the version Halderman diagnosed as highly vulnerable to attack and potential manipulation of results.
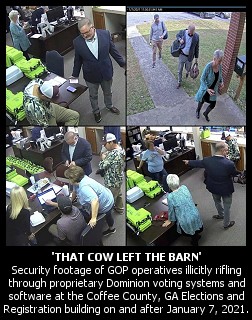
Dangerously, 5.5-A is also the version thoroughly pilfered by MAGA operatives organized (at least in sizable part) by Donald Trump lawyer Sidney Powell in what is known as the January 2021 Coffee County voting system breach. The intruders were allowed into the rural County's elections building by local GOP officials on multiple occasions to make unauthorized exact copies of the proprietary software still set for use across the entire state in 2024.
Following the breach, the intruders uploaded Dominion's 5.5-A software suite to a secret site on the Internet, allowing access to selected individuals and organizations who, themselves, may have further disseminated the swiped software. This code is currently used in jurisdictions in more than a dozen states across the country. Experts fear its release into unknown hands --- along with the federal judge's unsealing of the Halderman Report last month --- will allow "bad actors" plenty of time to plan attacks on the unpatched systems next year.
"It's a pretty bad breach," warned Richard DeMillo, founder of Georgia Tech's College of Cybersecurity on a recent episode of Pacifica Radio's The BradCast following the unsealing of Halderman's report on the Dominion BMD vulnerabilities. "We have letters from the new guy who took over the IT infrastructure in Coffee County that will absolutely curl your toes. He talks about machines not being patched for years."
DeMillo cited the breach as an example of how "bad actors" now may "know all the passwords and know how to access the machines, with their own axe to grind."
"The fact that there are people out there that have access to these software systems now and can experiment with them mean there are thousands, maybe tens of thousands of people, who have the ability to run the same kind of analysis that Alex Halderman did in his lab at the University of Michigan." Injecting results-altering malware into the system "has just been made mind-numbingly simple for an attacker."
On another recent BradCast episode, longtime elections expert Dr. Philip Stark, a PhD at the University of California in Berkeley, conceded that to "discover vulnerabilities and develop an attack takes some access." But, he cautioned, that access "has already been obtained by the people who were in the Coffee County elections office. They were there for weeks with uninterrupted access, they copied all the software from all of the devices."
"It was documented to the state that the equipment was being held in a room that had an unlocked exterior door, that the walls had holes in them, you could see daylight through the walls," Stark noted. "That's hardly physical security to keep the equipment safe. So getting access to these things for the purpose of developing malware, developing exploits, is really not hard. That cow left the barn."
(The BRAD BLOG is continuing its investigation of the ongoing cover-up of security and administrative failures and crimes related to the Coffee County breach which began just one day after the January 6, 2021 Trump-incited auto-coup attempt at the U.S. Capitol.)
Attempting to run the next election cycle using the widely shared stolen version from three years ago (5.5-A) would be gravely dangerous, say Raffensperger's critics. Even if the system were not exploited, experts charge that, in a close election, it would be difficult --- if not impossible --- to convince the public the election was free and fair, particularly since the voting system's overall opacity sometimes precludes a full understanding of debated details.
Therefore, although it remains unknown if the latest Dominion iteration actually plugs the holes discovered by Halderman (and perhaps by the Coffee County breachers and anyone else they gave or sold the software to), an upgrade would seem to make sense.
"That would be an improvement," argues Stark, who is also an expert for the plaintiffs along with Halderman, in the long-running Curling v. Raffensperger federal lawsuit seeking to ban the use of Georgia's touchscreen systems. But it's not close to enough, Stark insisted. "Going to hand-marked paper ballots as the default in polling places would be a much, much bigger improvement."
Out of time, fatal flaws, and hand-marked paper ballots
The Georgia Secretary of State is evidently running out of possible paths for maintaining his computerized voting status quo.
We asked Dominion spokeswoman Stephanie Walstrom if, for any version above 5.5-A, the company has sent to Raffensperger's office the letter of request Georgia law dictates must be submitted by the vendor to initiate the state certification process for election software.
"I don't have anything for you," she replied.
Making matters worse, while 5.5-A is compatible with Georgia's "poll pads," the electronic pollbooks used to check in voters and create cards allowing them to cast their ballots on a Dominion BMD at precincts, 5.17 is not currently compatible with them. That's according to Georgia's Deputy Election Director Michael Barnes at a June 21 hearing of the State Election Board.
As he explained the difficulties the Secretary of State's office is having in implementing the Dominion upgrade, Barnes confessed "the biggest surprise that we've encountered so far is the fact that the poll pads are not yet compatible with 5.17."
"The vendors are working together to resolve that," he told the Board, "but we don't yet have a timetable on how long that may take."
The politicians asking Raffensperger to update to Dominion Democracy Suite version 5.17 argue the vulnerabilities Halderman uncovered must be remedied. But without a state certification agent willing to officially weigh in on legal compliance, we now know the Georgia elections office currently cannot resolve Halderman's points by upgrading to 5.17. Even if they were able, the newest version 5.17 --- and the old 5.5-A iteration --- are both full of fatal problems.
"Raffensperger ignored the need to address the serious vulnerabilities and the Coffee breach even in the face of alarming information and early opportunities to address the elevated risk," charged Marilyn Marks, Executive Director of the Coalition for Good Governance, a nonprofit watchdog and plaintiff in the federal Curling case.
"Halderman delivered his report in July 2021 and DHS/CISA confirmed his findings in June 2022, recommending prompt mitigations," she continued. "Dominion's 5.17 update was available to Raffensperger's staff for testing and evaluation in October 2022. Throughout 2022 and early 2023 Raffensperger was aware of the massive statewide system breach that occurred in Coffee County and still delayed action until concluding that he would attempt no mitigations until at least 2025."
Even if he wanted to upgrade now, she asserted, U.S. District Judge Amy Totenberg has already determined certain attributes of the Dominion BMD system are in violation of state law. The certification testing wouldn't pass state muster.
In a 2020 ruling, for example, Totenberg determined the QR codes printed on each ballot by the touchscreen BMD system, used to record and tally votes, do not allow voters to verify their choices --- a violation of state law.
But, there is a solution that avoids all of these nightmares. "Current law requires hand-marked paper ballots as the back-up system when the electronic touchscreen system is impossible or impracticable for use," Marks told us. That is arguably the case right now.
"Hand-marked paper ballots can be counted by scanners --- which Georgia counties already have --- and then audited with robust, risk-limiting audits to determine that outcomes are correct. Hand-marked paper ballots are the way 70% of Americans vote. Georgians can too. It's a clear choice if they want far more secure and less controversial elections."
With additional reporting by Brad Friedman.
Originally from Texas, Douglas Lucas is a Seattle-based freelance writer/journalist, content marketer, and substitute teacher in public education. Besides speaking at a Buffalo, New York anarchist bookstore in 2017, he has reported from the trials of several federal defendants in the hacktivism/transparency movement, turned internal memos hacked out of the spy firm Stratfor into carefully researched stories, and appeared as an expert on the same in the documentary film The Hacker Wars. Visit his website, follow him on Twitter, or admire his houseplants on Instagram.


 Repub Support for Immigrants Skyrockets Amid Trump's Crackdown: 'BradCast' 7/14/25
Repub Support for Immigrants Skyrockets Amid Trump's Crackdown: 'BradCast' 7/14/25  Sunday 'Totally Predictable' Toons
Sunday 'Totally Predictable' Toons Democracy STILL Our Best Way Out of This Mess -- And Repubs Know It: 'BradCast' 7/10/25
Democracy STILL Our Best Way Out of This Mess -- And Repubs Know It: 'BradCast' 7/10/25 'Green News Report' 7/10/25
'Green News Report' 7/10/25
 'Mass Shooter Subsidy'?: More Dumb, Deadly Stuff in Trump's New Law: 'BradCast' 7/9/25
'Mass Shooter Subsidy'?: More Dumb, Deadly Stuff in Trump's New Law: 'BradCast' 7/9/25  Trump's New Law Supersizes ICE, Mass Detention, Militarization: 'BradCast' 7/8/25
Trump's New Law Supersizes ICE, Mass Detention, Militarization: 'BradCast' 7/8/25  'Green News Report' 7/8/25
'Green News Report' 7/8/25 Texas Flooding Tragedy Was Both Predictable and Predicted: 'BradCast' 7/7/25
Texas Flooding Tragedy Was Both Predictable and Predicted: 'BradCast' 7/7/25 Sunday 'Big Billionaire Bonanza' Toons
Sunday 'Big Billionaire Bonanza' Toons Sunday 'Total Obliteration' Toons
Sunday 'Total Obliteration' Toons 'Green News Report' 6/26/25
'Green News Report' 6/26/25 Thank You For Your Attention to This Matter:
Thank You For Your Attention to This Matter: Mamdani Primary 'Win' Augurs New Era of Rising Progressives: 'BradCast' 6/25/25
Mamdani Primary 'Win' Augurs New Era of Rising Progressives: 'BradCast' 6/25/25 U.S. Authoritarianism Under-way (But We're Still Here to Fight It): 'BradCast' 6/24/25
U.S. Authoritarianism Under-way (But We're Still Here to Fight It): 'BradCast' 6/24/25 'Anti-War' Trump Attacks Iran on False Claims About WMD: 'BradCast' 6/23/25
'Anti-War' Trump Attacks Iran on False Claims About WMD: 'BradCast' 6/23/25 Senate Health Care Cuts 'More Extreme' Than House Version: 'BradCast' 6/19/25
Senate Health Care Cuts 'More Extreme' Than House Version: 'BradCast' 6/19/25 What 'Anti-War President'? MAGA Civil War Over Trump, Iran: 'BradCast' 6/18/25
What 'Anti-War President'? MAGA Civil War Over Trump, Iran: 'BradCast' 6/18/25 Trump's 'Remigration' is Code for 'Ethnic Cleansing': 'BradCast' 6/17/25
Trump's 'Remigration' is Code for 'Ethnic Cleansing': 'BradCast' 6/17/25 Last Weekend Today: 'BradCast' 6/16/25
Last Weekend Today: 'BradCast' 6/16/25
 VA GOP VOTER REG FRAUDSTER OFF HOOK
VA GOP VOTER REG FRAUDSTER OFF HOOK Criminal GOP Voter Registration Fraud Probe Expanding in VA
Criminal GOP Voter Registration Fraud Probe Expanding in VA DOJ PROBE SOUGHT AFTER VA ARREST
DOJ PROBE SOUGHT AFTER VA ARREST Arrest in VA: GOP Voter Reg Scandal Widens
Arrest in VA: GOP Voter Reg Scandal Widens ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC
ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States'
LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States' 'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States
'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States FINALLY: FOX ON GOP REG FRAUD SCANDAL
FINALLY: FOX ON GOP REG FRAUD SCANDAL COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION
COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL
CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV
Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV  CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM
CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM
CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL
RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV
VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD
RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud
EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud GOP REGISTRATION FRAUD FOUND IN FL
GOP REGISTRATION FRAUD FOUND IN FL

































