Startling testimony offered by the U. of Michigan computer science professor whose team penetrated D.C.'s 'pilot program' server for what was to have been a live election beginning in just days...
 A University of Michigan computer scientist and his team were not the only ones attempting to hack the Internet Vote scheme that Washington D.C. had planned to roll out for actual use with military and overseas voters in this November's mid-term election.
A University of Michigan computer scientist and his team were not the only ones attempting to hack the Internet Vote scheme that Washington D.C. had planned to roll out for actual use with military and overseas voters in this November's mid-term election.
According to testimony given to a D.C. City Council committee last Friday by J. Alex Halderman, asst. professor of electrical engineering and computer science at University of Michigan, hackers from Iran and China were also attempting to access the very same network infrastructure, even as his own team of students had successfully done so, taking over the entirety of the Internet Voting system which had been opened for a first-of-its-kind live test.
[See our report last week on details of what had already been disclosed about Halderman's startling hack prior to last Friday's hearing.]
"While we were in control of these systems we observed other attack attempts originating from computers in Iran and China," Halderman testified. "These attackers were attempting to guess the same master password that we did. And since it was only four letters long, they would likely have soon succeeded."
In his stunning public testimony --- before a single member of the D.C. Board of Ethics and Elections (BoEE), and a nearly empty chamber --- Halderman explained how the team had, by the time they discovered their fellow intruders, already gained complete control of the system, it's encryption key and its passwords. The system was developed as part of an Internet Voting pilot program with the Open Source Digital Voting Foundation.
As The BRAD BLOG reported last week, Halderman's team was able to take over the system within 36 hours after it had gone live for testing. After having "found and exploited a vulnerability that gave [them] almost total control of the server software," his team was able to steal the encryption key needed to decode "secret" ballots; overwrite every single ballot cast on the test system; change the votes on those ballots to write-in candidates; discover who had already been voted for and the identities of the voters; install a script that would automatically change all votes cast in the future on the same system; install a backdoor to allow them to come back later; and then leave a "calling card" --- the University of Michigan fight song --- which was programmed to play in the voter's browser 15 seconds after each Internet ballot had been cast.
But the new disclosures offered before the committee on Friday, including the hack attempts by computers in China and Iran, may have been as explosive, if not more so, than the previous revelations. They certainly illustrate and underscore a grave national security threat present in electronic voting systems such as the one D.C. had planned to use, as Lawrence Livermore National Laboratories computer scientist and cyber-security expert Dr. David Jefferson told me during an interview last Friday night on the nationally syndicated Mike Malloy Show which I was guest hosting last week.
The hack of the system forced the D.C. election administrators to shut down their plans for the pilot program which was to have gone live in days, as encouraged and partially funded by the federal Military and Overseas Voter Empowerment (MOVE) Act, which allocated millions of dollars for such Internet Voting pilot programs.
The revelations of the intrusion attempts from China and Iran, however, would not be the only new, previously unreported bombshells Halderman offered during his Friday testimony...
--- Click here for REST OF STORY!... ---
 I'm no good at raising money for The BRAD BLOG - so let's see if I have any better luck helping out progressive filmmaker John Wellington Ennis to complete his newest documentary, Pay 2 Play: Democracy's High Stakes, covering the Supreme Court's Citizens United disaster and other related bastardizations of our democracy by the highest corporate bidder.
I'm no good at raising money for The BRAD BLOG - so let's see if I have any better luck helping out progressive filmmaker John Wellington Ennis to complete his newest documentary, Pay 2 Play: Democracy's High Stakes, covering the Supreme Court's Citizens United disaster and other related bastardizations of our democracy by the highest corporate bidder.

 Blowing Smoke.
Blowing Smoke. 'Green News Report' 5/6/25
'Green News Report' 5/6/25
 SCOTUS Allowing Publicly-Funded Religious Schools 'Would be a Ground-Breaking Disaster': 'BradCast' 5/7/25
SCOTUS Allowing Publicly-Funded Religious Schools 'Would be a Ground-Breaking Disaster': 'BradCast' 5/7/25 Trump Judge Blocks NC GOP Attempt to Steal 2024 State Supreme Court Election: 'BradCast' 5/6/25
Trump Judge Blocks NC GOP Attempt to Steal 2024 State Supreme Court Election: 'BradCast' 5/6/25 Prosecutors Resign After Trump U.S. Attny Strikes Deal With Felon Cop: 'BradCast' 5/5/25
Prosecutors Resign After Trump U.S. Attny Strikes Deal With Felon Cop: 'BradCast' 5/5/25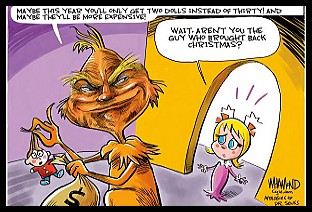 Sunday 'Good Buy, Dolly!' Toons
Sunday 'Good Buy, Dolly!' Toons Trump Losing Streak Continues into SECOND Hundred Days: 'BradCast' 5/1/25
Trump Losing Streak Continues into SECOND Hundred Days: 'BradCast' 5/1/25 'Green News Report' 5/1/25
'Green News Report' 5/1/25 100 Daze: 'BradCast' 4/30/25
100 Daze: 'BradCast' 4/30/25 Campaign to 'Impeach Trump Again' Gains Fresh Momentum: 'BradCast' 4/29/25
Campaign to 'Impeach Trump Again' Gains Fresh Momentum: 'BradCast' 4/29/25 'Green News Report' 4/29/25
'Green News Report' 4/29/25 And Then They Came for the Judges...: 'BradCast' 4/28/25
And Then They Came for the Judges...: 'BradCast' 4/28/25 Sunday 'Desperation' Toons
Sunday 'Desperation' Toons Trump EPA Guts Enviro Justice Office: 'BradCast' 4/24/25
Trump EPA Guts Enviro Justice Office: 'BradCast' 4/24/25 'Green News Report' 4/24/25
'Green News Report' 4/24/25 Sunday
Sunday  Largest U.S. Broad-caster Hoaxes Viewers to Help Gut FCC Rules: 'BradCast' 4/23/25
Largest U.S. Broad-caster Hoaxes Viewers to Help Gut FCC Rules: 'BradCast' 4/23/25 FCC on Precipice of Ending All Limits on Corp. Control of Local TV Stations
FCC on Precipice of Ending All Limits on Corp. Control of Local TV Stations GOP Earth Day 2025 Hypocrisies and Dilemmas: 'BradCast' 4/22/25
GOP Earth Day 2025 Hypocrisies and Dilemmas: 'BradCast' 4/22/25 Pope Francis Dies, Trump Still Alive and Criming: 'BradCast' 4/21/25
Pope Francis Dies, Trump Still Alive and Criming: 'BradCast' 4/21/25 Soc. Sec. Expert Warns DOGE of Collapse, Privatization: 'BradCast' 4/10/2025
Soc. Sec. Expert Warns DOGE of Collapse, Privatization: 'BradCast' 4/10/2025 Trump Blinks, Chaos Reigns, Markets Spike Amid Tariff 'Pause': 'BradCast' 4/9/25
Trump Blinks, Chaos Reigns, Markets Spike Amid Tariff 'Pause': 'BradCast' 4/9/25 SCOTUS Deportation Ruling Grimmer Than First Appears: 'BradCast' 4/8/25
SCOTUS Deportation Ruling Grimmer Than First Appears: 'BradCast' 4/8/25 Cliff Diving with Donald: 'BradCast' 4/7/25
Cliff Diving with Donald: 'BradCast' 4/7/25
 VA GOP VOTER REG FRAUDSTER OFF HOOK
VA GOP VOTER REG FRAUDSTER OFF HOOK Criminal GOP Voter Registration Fraud Probe Expanding in VA
Criminal GOP Voter Registration Fraud Probe Expanding in VA DOJ PROBE SOUGHT AFTER VA ARREST
DOJ PROBE SOUGHT AFTER VA ARREST Arrest in VA: GOP Voter Reg Scandal Widens
Arrest in VA: GOP Voter Reg Scandal Widens ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC
ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States'
LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States' 'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States
'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States FINALLY: FOX ON GOP REG FRAUD SCANDAL
FINALLY: FOX ON GOP REG FRAUD SCANDAL COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION
COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL
CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV
Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV  CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM
CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM
CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL
RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV
VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD
RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud
EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud GOP REGISTRATION FRAUD FOUND IN FL
GOP REGISTRATION FRAUD FOUND IN FL



















 The Connecticut State Election Commission announced this morning in Hartford that "it cannot make a full and fair determination of the allegations" against Ann Coulter who was alleged to have committed voter fraud twice in the state by voting illegally from her residence in New York City while being registered at her parents home in the Nutmeg State.
The Connecticut State Election Commission announced this morning in Hartford that "it cannot make a full and fair determination of the allegations" against Ann Coulter who was alleged to have committed voter fraud twice in the state by voting illegally from her residence in New York City while being registered at her parents home in the Nutmeg State.



 If American politics and political discourse is going to devolve into little more than a bad Disney cartoon --- and it has, as this election season demonstrates in spades --- why not just cut out the middle man and cut straight to the cartoon chase?
If American politics and political discourse is going to devolve into little more than a bad Disney cartoon --- and it has, as this election season demonstrates in spades --- why not just cut out the middle man and cut straight to the cartoon chase? Just in. Yet another in the recent string of victories for (real) conservative values and the U.S. Constitution...
Just in. Yet another in the recent string of victories for (real) conservative values and the U.S. Constitution...
 A University of Michigan computer scientist and his team were not the only ones attempting to hack the Internet Vote scheme that Washington D.C. had planned to roll out for actual use with military and overseas voters in this November's mid-term election.
A University of Michigan computer scientist and his team were not the only ones attempting to hack the Internet Vote scheme that Washington D.C. had planned to roll out for actual use with military and overseas voters in this November's mid-term election.  We're back tonight to close out the week, filling in as guest-host on the nationally syndicated
We're back tonight to close out the week, filling in as guest-host on the nationally syndicated 

 Will Ann Coulter finally be held accountable for having committed voter fraud? We may find out on October 14th when the matter will come up at a public hearing by Connecticut's State Elections Commission after an extraordinarily long two-year delay since the complaints about her allegedly illegal absentee votes in 2002 and 2004 were filed.
Will Ann Coulter finally be held accountable for having committed voter fraud? We may find out on October 14th when the matter will come up at a public hearing by Connecticut's State Elections Commission after an extraordinarily long two-year delay since the complaints about her allegedly illegal absentee votes in 2002 and 2004 were filed. As we
As we It took nearly a week of
It took nearly a week of 












