 Plaintiffs in a Georgia lawsuit seeking to force the state to move to a hand-marked paper ballot system in time for this year's midterm elections, promise to produce expert testimony to the court, demonstrating that "Georgia's voting system is a catastrophically open invitation to malicious actors intent on disrupting our democracy."
Plaintiffs in a Georgia lawsuit seeking to force the state to move to a hand-marked paper ballot system in time for this year's midterm elections, promise to produce expert testimony to the court, demonstrating that "Georgia's voting system is a catastrophically open invitation to malicious actors intent on disrupting our democracy."
The Coalition for Good Governance and a group of multi-partisan individual plaintiffs filed a motion [PDF] on July 31, seeking a preliminary injunction in the federal case, to prevent Georgia from conducting this year's midterms on the state's notorious Diebold AccuVote TS (touchscreen) Direct Recording Electronic (DRE) voting machines. Instead, plaintiffs seek an order that Georgia's election officials utilize, for in-person voting, the same already-certified, Diebold paper ballot-based optical-scan system currently used for tabulation of the Peach State's absentee ballots.
Last week, U.S. District Court Judge Amy Totenberg ordered an expedited briefing schedule on plaintiffs' motion to compel the State of Georgia to adopt this simple method for conducting a verifiable paper ballot election on November 6, 2018.
The plaintiffs cite a massive body of scientific evidence finding the 100% unverifiable Diebold touchscreen systems as essentially electronic black holes, prone to unintended systemic failures and vulnerable to all manner of undetectable malicious manipulation by insiders or anyone else who acquires minimal access to the system or any of its machines. They also point to evidence that the statewide system was previously compromised via the Internet. Plaintiffs argue the 16-year old system deprives the electorate of their constitutional right not only to cast a vote but to have their vote accurately counted.
Recognizing "the gravity and importance of the constitutional issues," the court directed the parties (principally GA Secretary of State Brian Kemp, the state's GOP nominee for governor), as well as the plaintiffs to address "the practical realities surrounding implementation of the requested relief in the next one to three months." Judge Totenberg asks defendants to address the "practical realities" issue in a response by August 14. Plaintiffs' reply is then due by August 20.
The question before the court is monumental and could help set a precedent across the country in other jurisdictions where voters are forced to use unverifiable touchscreens on Election Day, rather than a paper ballot system that is already available via the absentee systems used in all 50 states.
As we documented last year, in "Why Do Georgia Election Officials Insist on 100% Unverifiable Elections?", if the court issues the preliminary injunction, November 6, 2018 would mark the first time in more than a decade and a half that the State of Georgia will have held an election in which it will be possible for human beings to verify or refute the accuracy of an electronic vote tally, thanks to the use of hand-marked paper ballots...
Scientific studies
In his declaration supporting the plaintiff's motion, Matthew D. Bernhard, a University of Michigan PhD candidate in computer science, points to numerous academic studies, dating back to 2004, which document all manner of Diebold DRE vulnerabilities to external hacking, systemic failures and malicious insider manipulation --- many of which have been reported upon by (and even initially broken by) The BRAD BLOG over the past 14 years. Those studies include, but are not limited to, the 2006 "Princeton Hack" and California's 2007 "Top-to-Bottom" review. The latter occasioned a decision by then CA Secretary of State Debra Bowen to decertify the Diebold DRE systems still used in Georgia over a decade later, after the landmark study revealed all manner of vulnerabilities to both systemic errors and malicious manipulation that could undetectably alter the outcome of elections.
(Bernhard overlooked a 200-page report prepared by Scientific Applications International Corp. ("SAIC") in 2003 at the behest of the Maryland Board of Elections. That report was subsequently reduced to 38-pages, redacted and altered under the aegis of MD's still-serving Elections Administrator Linda Lamone so as to conceal, not only from the public but also from Maryland's governor, the full report's condemnation of the unacceptable vulnerabilities of the unverifiable Diebold DREs. After the full SAIC report, which identified some 180 security flaws, was obtained and released in 2006 by The BRAD BLOG, it was described as the "Pentagon Papers of Electronic Voting Systems." This was followed by a 20 to 3 vote by the MD House Ways and Means Committee to scrap the Diebold DREs. Maryland, which, with Georgia was first in the nation to deploy the systems in 2002, has since moved to a paper ballot system. Georgia has not.)
All methods of computerized tabulation --- of paper ballots or electronic votes --- are vulnerable to malicious manipulation, systemic failures and/or unintended error. Unlike paper ballot-based optical-scan systems, however, DRE systems are especially troubling because it is literally impossible to measure the accuracy of a DRE machine count.
"A voter has no way of independently verifying that the button they touched on the screen is what the machine recorded in memory," Bernhard notes in his declaration. "If the system is not correctly recording votes, either in error or out of malice, there is no way to tell."
Previously compromised
Last year, Politico published an explosive article by Kim Zetter, revealing that in August of 2016, Logan Lamb, a 29-year old former cybersecurity researcher at the U.S. Oakridge National Laboratory, logged onto the Kennesaw State University's Center for Election Security (CES) website. At that time, CES was contracted by Georgia, at a cost to taxpayers of $800,000 per year, to test and program the entirety of Georgia's electronic voting, voter registration and tabulation systems for each and every election.
Hoping to retrieve a few documents that would facilitate an understanding of the security procedures at CES, "Lamb wrote an automated script to scrape the site" and left for lunch. "When he returned," Zetter reported, Lamb "discovered that the script had downloaded 15 gigabytes of data", a "mother lode" that included "registration records for the state's 6.7 million voters; multiple PDFs with instructions and passwords for election workers to sign in to a central server on Election Day," and access to the database of GEMS, the computer system which, among other tasks, is used to "tabulate votes and produce summaries of vote totals."
During that same month, August 2016, just before that year's Presidential election, Georgia's Secretary of State, Brian Kemp, "refused" to accept a U.S. Department of Homeland Security (DHS) offer to assist states in securing the integrity of their respective elections systems, according to the complaint. Kemp, plaintiffs alleged, claimed that the Obama Administration's DHS offer amounted to an attempt to "subvert the Constitution to achieve the goal of federalizing elections under the guise of security."
To this day, Georgia DREs continue to run a Diebold-modified version of Microsoft's Windows CE 4.1 which Microsoft no longer supports. "As the operating system is over twenty years old," according to Bernhard, "it lags behind two decades of computer science security research and is extremely vulnerable to a wide variety of attacks that Diebold's software, regardless of version, cannot defend against."
Where the 2006 "Princeton hack" revealed that a lone malicious actor with as little as one minute's direct access to a Diebold touchscreen machine could implant a virus via a memory card that could undetectably rig an entire Diebold touchscreen election, Lamb discovered that a malicious hacker, using the Internet, could gain "control of the [CES] server [and then] modify files that are downloaded by the end users of the website, potentially spreading malware to everyone who downloaded files from the website."
Although Lamb directly notified CES's executive director Merle King via an August 28, 2016 email that the system was compromised, it wasn't until late February 2017 that Lamb learned from a colleague, Chris Grayson, that CES had failed to remediate these critical security issues. Thus, in their new motion, the plaintiffs observe that "between at least August 2016 and March 2017, and likely for a much longer time, this server was fully accessible to any computer user with Internet access."
In the wake of Lamb's revelations last year and subsequent legal action, the responsibility for testing and programming Georgia's 100% unverifiable voting system was transferred from CES to the office of Georgia's Republican Secretary of State Brian Kemp. Nonetheless, the system remains wildly vulnerable to a malicious Internet-based attack.
The gravity of these vulnerabilities is underscored by the July 13, 2018 indictment filed against 12 members of Russia's military intelligence agency, the GRU, laying out the dates and specific manner in which named individuals are said to have carried out cyberattacks directed at U.S. elections. The indictment alleges that in October 2016 the GRU "targeted state and county offices responsible for the 2016 U.S. election. For example, on or about October 28, 2016 [the GRU] visited the websites of certain counties in Georgia, Iowa and Florida to identify vulnerabilities." In November, 2016, the GRU "sent over 100 spearphishing emails" to Florida election administrators.
Those concerns are amplified back by a March 15, 2018 joint tactical alert issued by DHS and the Federal Bureau of Investigation (FBI). The Alert publicly revealed that, commencing no later than March 2016, Russian government cyber actors ("threat actors") began "targeting U.S. Government entities as well as organizations in the energy, nuclear, commercial facilities, water, aviation, and critical manufacturing sectors." This involved a "multi-stage intrusion campaign" in which the Russian threat actors "targeted small commercial facilities' networks where they staged malware, conducted spearphishing and gained remote access into energy sector networks."
In the Georgia complaint, Bernhard, who refers to these sophisticated professional government hackers as "Advanced Persistent Threat Actors" (APTs), declared that "it is extremely likely that APTs are trying to access and manipulate election systems. Given the level of vulnerability present in Georgia's voting system," he adds, "it is a near certainty that if an APT has tried to get in, it has succeeded." Bernhard knows this because, he notes, he has personally "gained access to Georgia's election system."
Sea change
Computer scientists and election integrity advocates have long recognized a wide range of potential threats posed by the use of DREs that have nothing to do with the Internet. These include the ability of a malicious actor to effectuate undetectable wholesale changes with minimal physical access to a Diebold memory card, the GEMS central tabulator or any one of the DRE machines. "Demonstrations show that it is easy to break into AccuVote TSXs with nothing more than a BIC pen and install vote-stealing software that changes votes in undetectable ways," plaintiffs note in their motion.
Indeed, over this past weekend, at this year's DefCon hackers convention in Las Vegas, where a number of voting and tabulation systems were on display for hands-on investigation, Susan Greenhalgh, Policy Director at the National Election Defense Coalition, observed that "when opening a Diebold voting machine" similar to those used in Georgia, the hackers "didn't have the right tools so they used a pen."
Bernhard, who notes in his affidavit that the GA machines use the same key that is commonly used for hotel mini-bars (as we first reported back in 2006), observed additional physical security flaws when he was afforded unsupervised access to the Fulton County Election Preparation Center ("EPC") in Atlanta. The EPC is responsible for programming, servicing and storing all of Fulton County's DRE machines. Yet, Bernhard asserts, EPC lacks the "operational security necessary to protect Georgia's machines from tampering."
Bernhard saw "stacks of voter access and supervisor cards that could easily be stolen"; "printouts of password sheets" that were "pasted all over the facility", and "stacks of memory cards [that] were strewn about during the election programming process, as many of the cards are programmed at once using card replicators." If "a virus were present on even one of these memory cards," Bernhard argues, "the card replicators could spread [the virus] more quickly than even imagined in the Princeton study."
Voting on these vulnerable, yet 100% unverifiable DREs amounts to an exercise in blind faith. That fact alone would have justified their rejection in 2002, when Diebold first sold its machines to Georgia. Yet, as revealed by the newly filed motion, during the pivotal 2016 Presidential Election, nationwide, approximately 20% of the American electorate deposited their votes into these and similar electronic black holes.
In the past, that reality has largely been marginalized by the U.S. corporate media and, to an extent, by the U.S. judiciary. But, thanks to Congressional investigations and the ongoing media coverage of U.S. Intelligence Community and FBI counterintelligence assessments following the 2016 election, there has been a sea change in both governmental and public awareness of the threat posed by continued use of DREs.
The significance of that sea change has not been lost on plaintiffs' attorneys in the case now before Judge Totenberg. They note that a Congressional Task Force on Election Security and the Senate Select Committee on Intelligence both recognized that DRE's pose an unacceptable risk. DHS Secretary Kirstjen Nielsen labeled the unverifiable touchscreens as a "national security concern." Even Trump Administration apologist and protector, Rep. Devin Nunes (R-CA), Chairman of the House Intelligence Committee, "joined many federal officials and agencies concerned with national security to call for a complete ban on electronic voting," according to the pending motion.
Building upon the ominous observation made by Dan Coats, Trump's Director of National Intelligence, that "the warning lights are blinking red again" with respect to the prospect of Russian election-related cyberattacks, plaintiffs' counsel directly quote Coats as stating:
From this, counsel wrap-up their motion by offering to present expert testimony during the hearing on the motion for the preliminary injunction to demonstrate that "Georgia's voting system is a catastrophically open invitation to malicious actors intent on disrupting our democracy."
Systemic failures, anomalous results
In their motion, the Curling plaintiffs point to systemic failures from recent elections. These include electronic pollbooks that contained inaccurate party designations and inaccurate voter eligibility information that "caused potential and actual disenfranchisement;" a DRE electronic ballot that displayed the "wrong districts and candidates during early voting," and "unauthorized changes in voter registration records." There were "unresolved material differences between the number of voters voting at the polling place and the number of ballots cast as reporting on the DRE machine results tapes," according to declarations filed in support of the motion.
As McClatchy recently detailed, reporting on the same lawsuit, "It appeared, according to the Georgia Secretary of State's website, that Habersham County's Mud Creek precinct in northeastern Georgia had 276 registered voters ahead of the state's primary elections in May. ... Some 670 ballots were cast, according to the Georgia secretary of state's office, indicating a 243 percent turnout."
In another instance cited by plaintiffs, "a Hall County voting machine malfunctioned, was taken out of service and showed no votes cast...Poll workers...disagreed on whether votes were cast on the problem machine."
Last year, we noted how, following the 2002 privatization of Georgia's public election system and Diebold's covert insertion of illegal software patches on some 5,000 AccuVote TS touchscreens in two heavily Democratic counties, the November 2002 election produced some of the statistical anomalies that have now become so commonplace in modern American elections, particularly where 100% unverifiable e-voting systems are involved.
Six days before the November 2002 general election, polls showed Sen. Max Cleland, a decorated war veteran and Democratic incumbent, leading his Republican opponent Saxby Chambliss by five percentage points. With their new 100% unverifiable Diebold systems in place, Georgia ultimately declared that Chambliss received 53% of the vote to Cleland's 47% --- a twelve-point turn around. In the Governor's race the same year, the same statewide polls showed Democrat Roy Barnes leading by a whopping 11% before the election. The Diebold touchscreen system, however, declared his Republican opponent, Sonny Perdue, had won 51% of the vote.
Were those suprising 2002 results inaccurate or did they reflect an unexplained last minute change in the mood of the electorate? Nobody can ever know, thanks to GA's unverifiable DRE system.
Those statistical anomalies pale in comparison, however, to what took place this year with respect to Georgia's selection of a Republican nominee for governor.
According to the official results, during the May 24 primary, 607,874 GA Republicans cast votes on who should serve as their Party's candidate for Governor. Lt. Gov. Casey Cagle received 236,371 or 38.9% of the vote. Scarcely more than one in every four Republican voters (155,324 or 25.6%) preferred Secretary of State Brian Kemp as the party's nominee.
As no candidate received more than 50% of the vote, a primary runoff was held in July. This time around, according to the official count, only 585,550 Republicans voted --- 22,324 less than the number who voted during the May 24 primary. Where slightly more than one-in-four Republicans voted for Kemp in May, just two months later nearly seven out of every ten Republicans (69%) voted for Kemp --- 406,667 of the 585,550 Republicans who weighed in, according to the computer-reported results.
Cagel's raw vote total (178,883) was 57,488 less than the total he received during the May 24 primary. That result could be sustained only if we assume that (a) every one of the 22,324, who did not vote during the July 24 runoff, had cast their vote for Cagel on May 24; (b) everyone, who voted for someone other than Cagel or Kemp in the primary voted for Kemp in the July runoff, and (c) after just two months, approximately 35,000 Republicans switched their votes from Cagel to Kemp.
Last year, after it was revealed that Georgia's e-voting system, then managed by CES, had been compromised, direct responsibility for testing and programming the entirety of Georgia's electronic voting, voter registration and vote tabulation systems was transferred from CES to Kemp's own office as Secretary of State. Thus, Kemp's office had direct access to the easily manipulated and unverifiable Diebold touchscreens at the time of the ensuing July 24, 2018 Cagle v. Kemp Republican gubernatorial runoff.
'Practical realities'
In their motion, plaintiffs took a comparative approach to their proposed remedy of switching immediately to hand-marked paper ballots. It would be far simpler to transition to the already-certified, paper ballot optical-scan system than it would be to try and repair the fatally compromised DRE system.
To ensure that the DRE system is no longer compromised, Georgia would have to undergo what Bernhard describes as a "massive time-consuming effort." The state would have to retain "experienced technicians to give hands-on attention to individual machines (tens of thousands of pieces of equipment), one at a time." Even then the effort would likely prove futile as each piece of equipment would still be vulnerable to a new attack (and still wholly unverifiable to the public afterwards, in any event.)
More detail, however, is needed to demonstrate the simplicity of the proposed remedy. Obviously, since Georgia already prints optical-scan readable paper ballots for absentee voters, it should not be difficult for the state to print a sufficient number of additional paper ballots for all voters. Moreover, we have been advised by one of the plaintiffs that Georgia has as many as 1,000 available Diebold optical scanners. It is unclear whether that is sufficient to place a scanner at each precinct, but the number is obviously sufficient to centrally tabulate the votes at county headquarters. Large jurisdictions such as Los Angeles County in California, with some 4.3 million registered voters, do the same. Plaintiffs can delineate strict chain-of-custody procedures for ensuring the integrity of the optical-scan readable paper ballots, along similar lines for the chain-of-custody procedures already in place for delivering electronic memory cards from precincts to county headquarters. The court should include those procedures in its order.
Because it would finally open up the possibility for human beings to verify or refute the accuracy of a computer tally, replacing the DREs with a paper-based optical-scan system would mark a significant step towards more transparent and fully verifiable elections in Georgia. Both Diebold DREs and optical-scan systems feed voting data into a GEMS central tabulator. Like all other e-voting systems, the GEMS tabulator is vulnerable to unintended error and/or malicious manipulation capable of wholesale changes to vote tabulation. Indeed, in a declaration filed in support of the motion, Logan Lamb --- the security researcher who discovered the state voter registration database and system passwords lying around for the taking on the CES website --- noted that the remaining "components of the Diebold system, such as the GEMS server, AccuVote optical scanners, and the Express Vote electronic pollbooks must undergo decontamination procedures prior to use in future elections."
Election integrity will only be fully achieved in the U.S. after either Congress or our courts follow the lead of Germany's highest court, which, in 2009, banned all forms of e-vote tabulation. There's an elegantly simple and inexpensive 19th century solution to 21st century e-vote vulnerability: hand-marked paper ballots, publicly hand-tallied with the results posted at each precinct on election night before those paper ballots are transferred elsewhere. Brad Friedman aptly described this solution as "Democracy's Gold Standard." It is a transparent, publiclly overseeable system that has been successfully deployed by several towns in New Hampshire over many years. Those towns often complete their transparent and verifiable counts more swiftly than their machine-counting counterparts.
Plaintiffs would do well to propose "Democracy's Gold Standard" as an eventual alternative to the proposed optical-scan system, leaving it to the court to determine which would be best suited given the relatively short time between now and the November 6 election. Either way, hand-marked paper ballots, remain the bedrock baseline for any overseeable election in America's representative democracy. Such a system is long overdue to the voters in the great state of Georgia. This current court case represents a golden opportunity for a major step toward that end and, as plaintiffs argue, it can easily be done in time for this November's midterms.
UPDATE, 8/29/18: On August 28, Judge Totenberg issued an order in which she denied the defendants' motions to dismiss plaintiffs' third amended complaint and in which she scheduled a hearing on the motion for the preliminary injunction for September 27, 2018.
 Ernest A. Canning is a retired attorney, author, Vietnam Veteran (4th Infantry, Central Highlands 1968) and a Senior Advisor to Veterans For Bernie. He has been a member of the California state bar since 1977. In addition to a juris doctor, he has received both undergraduate and graduate degrees in political science. Follow him on twitter: @cann4ing
Ernest A. Canning is a retired attorney, author, Vietnam Veteran (4th Infantry, Central Highlands 1968) and a Senior Advisor to Veterans For Bernie. He has been a member of the California state bar since 1977. In addition to a juris doctor, he has received both undergraduate and graduate degrees in political science. Follow him on twitter: @cann4ing


 Week 8: Iran War Lies Continue from Sundowning Gaslighter-in-Chief: 'BradCast' 4/20/26
Week 8: Iran War Lies Continue from Sundowning Gaslighter-in-Chief: 'BradCast' 4/20/26 Sunday 'WWJD?' Toons
Sunday 'WWJD?' Toons U.S. Middle Eastern 'War Crimes' Then and Now: 'BradCast' 4/16/26
U.S. Middle Eastern 'War Crimes' Then and Now: 'BradCast' 4/16/26 'Green News Report' 4/16/26
'Green News Report' 4/16/26
 Trump's USDA Takes Chainsaw to U.S. Forest Service: 'BradCast' 4/15/26
Trump's USDA Takes Chainsaw to U.S. Forest Service: 'BradCast' 4/15/26 Midterm Elections Reality Check:
Midterm Elections Reality Check: 'Green News Report' 4/14/26
'Green News Report' 4/14/26 Another Mad, Mad, Mad, Mad Weekend: 'BradCast' 4/13/26
Another Mad, Mad, Mad, Mad Weekend: 'BradCast' 4/13/26 Sunday 'Mission Accomp...' Toons
Sunday 'Mission Accomp...' Toons MAGA Buckles: 'BradCast' 4/9/26
MAGA Buckles: 'BradCast' 4/9/26 'Green News Report' 4/9/26
'Green News Report' 4/9/26 Chaos, 'Ceasefire' Politics, Iran with Upper Hand: 'BradCast' 4/8/26
Chaos, 'Ceasefire' Politics, Iran with Upper Hand: 'BradCast' 4/8/26 Bye Bye Bondi (and It's TACO Tuesday Again!): 'BradCast' 4/7/26
Bye Bye Bondi (and It's TACO Tuesday Again!): 'BradCast' 4/7/26 Trump Unhinging: 'BradCast' 4/6/26
Trump Unhinging: 'BradCast' 4/6/26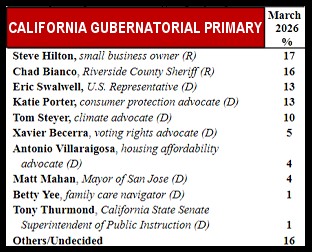 Potential Disaster for Democracy in Deep 'Blue' CA
Potential Disaster for Democracy in Deep 'Blue' CA BRAD BLOG on the Move: Some good news for a happy change!...
BRAD BLOG on the Move: Some good news for a happy change!... Trump Over a Barrel on Iran: 'BradCast' 3/25/26
Trump Over a Barrel on Iran: 'BradCast' 3/25/26 'Holding Out Hope' for SCOTUS on Late Mail Ballots: 'BradCast' 3/24/26
'Holding Out Hope' for SCOTUS on Late Mail Ballots: 'BradCast' 3/24/26 FCC Chair Follows Instructions, Approves Unlawful Merger: 'BradCast' 3/23/26
FCC Chair Follows Instructions, Approves Unlawful Merger: 'BradCast' 3/23/26
 VA GOP VOTER REG FRAUDSTER OFF HOOK
VA GOP VOTER REG FRAUDSTER OFF HOOK Criminal GOP Voter Registration Fraud Probe Expanding in VA
Criminal GOP Voter Registration Fraud Probe Expanding in VA DOJ PROBE SOUGHT AFTER VA ARREST
DOJ PROBE SOUGHT AFTER VA ARREST Arrest in VA: GOP Voter Reg Scandal Widens
Arrest in VA: GOP Voter Reg Scandal Widens ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC
ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States'
LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States' 'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States
'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States FINALLY: FOX ON GOP REG FRAUD SCANDAL
FINALLY: FOX ON GOP REG FRAUD SCANDAL COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION
COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL
CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV
Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV  CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM
CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM
CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL
RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV
VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD
RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud
EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud GOP REGISTRATION FRAUD FOUND IN FL
GOP REGISTRATION FRAUD FOUND IN FL

































